It’s no secret that WordPress is the most popular content management system (CMS) on the web.
In fact, as of 2018, WordPress now powers 30% of all online websites.
While this is truly a major feat for the popular CMS that began as a blog publishing platform, there is a disastrous plague that is infecting thousands of WordPress sites.
Hackers are now rapidly succeeding at infiltrating WordPress sites, and they’re doing so at an alarming rate.
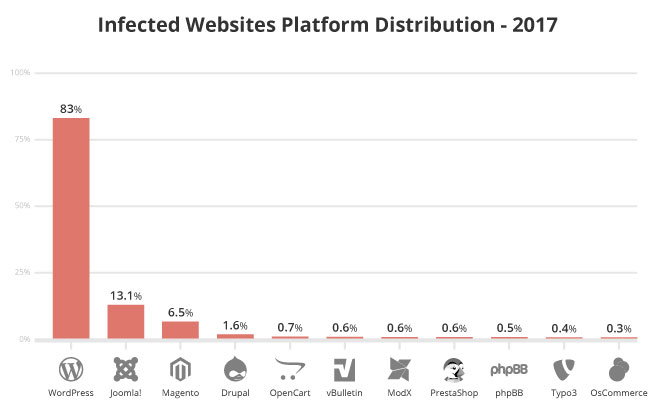
Just take a look at this report from Sucuri that included data from over 30,000 websites.
You don’t have to rub your eyes in disbelief.
WordPress is responsible for 83% of the total of infected websites in 2017.
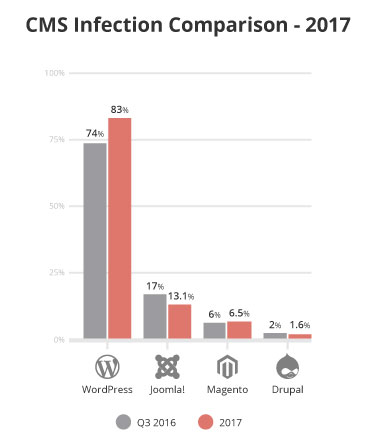
This trend hasn’t just started either.
In 2012, over 117,000 WordPress sites were hacked.
As you can see in the above graph, more websites may be in trouble now.
This might even be a fact since the number of WordPress websites being hacked has increased year-to-year.
For a CMS that claims to power 30% of the internet, this level of insecurity is frightening, especially for small businesses.
It doesn’t take a rocket scientist to know the wide-reaching effects of being hacked.
Not only does having your website hacked place your information and your customers’ data in the hands of criminals, but a hacker can ruin all of the time and money you placed into your website within just a few minutes.
To spare you this unpleasant experience, it’s time you know that your website isn’t secure with WordPress.
And, in this article, I’m going to tell you why.
Why Do Hackers Target WordPress Sites

Many small businesses naturally believe that they will never become hacking targets.
After all, why would any hacker care about your blog or your website’s content? What could these hackers possibly gain from compromising it?
In reality, hackers don’t really care about your web traffic or even your online popularity.
Allow me to explain why.
The first thing to understand is that hackers often don’t premeditate their attacks. Many sites get hacked simply because it’s possible.
Unless you’re running a billion-dollar corporation like Sony or Walmart, a hacker usually won’t have a specific reason for why they’re attacking your site.
For many small businesses, hackers make their attacks because these businesses allow them to.
Therefore, it’s truly not about whether it makes sense to hack your site, or even how small or insignificant your site is compared to others.
If you are using WordPress, your site is likely unsecure.
Thus, you’ll always be a viable target for hackers.
To make matters worse, hackers are becoming smarter by taking advantage of complacent websites that may not know that they are unsecure.
Most hackers unleash automated attacks by sending bots to crawl the web to look for sites with security issues.
If your website is found by these bots, your security could instantly be compromised.
Of course, e-commerce sites process sensitive financial data, such as credit cards and even PayPal information.
If hackers get their hands on this data, they can assume your customers’ identities, and this can extremely damage your site’s credibility.
Normal websites aren’t off the hook, either.
Hackers can access these websites in the following ways:
- Drive-by-downloads - Hackers can use your website to infect the computers of anyone that visits your site with malware that includes viruses, back doors, key trackers, or other malicious software to steal data they can use for their own gain.
- Redirections - Sometimes hackers will subtly infect your website so that your website visitors are redirected to other websites that will generate affiliate income for them.
- System Resources - Hackers can also take control of your server and use it to send spam emails, perform a denial of service, or engage in brute force attacks that can steal your web visitors’ private information. Eventually, these attacks can cause your server and your site to be blacklisted, and it can also increase the cost of your hosting if it’s based on usage.
Hackers have an uneven playing field against unsecured WordPress websites.
Want to know how these hackers can access your site? Then keep reading... because the answer will shock you.
How Do Hackers Access WordPress Sites?

WordPress is an open-source software, which is just a fancy term that means that volunteers (like you and me) can access and modify WordPress’ code.
Of course, this is a good thing for WordPress users, because it means that members of the WordPress community can create useful third-party plugins that anyone can use.
Nonetheless, this is also a VERY BAD thing for WordPress users as well.
And, the cons of this open-source software far outweigh the pros.
As I said, anyone can access and modify WordPress’ code, so third-party plugins can become vulnerable to hackers.
That means you, and any other WordPress site that uses these plugins could be in danger of being hacked.
This is especially true if these plugins aren’t updated. Hackers love finding weaknesses in WordPress sites that aren’t updated.
Also, Hackers are always finding ways to exploit open-source software, so WordPress may not be an ideal option for small businesses that want to avoid being hacked.
If any of this news scares you or reignites a fire in you to protect your business from savvy hackers, then that’s great!
Here’s what you can do to maximize your site’s security and prevent hackers from compromising your data.
Optuno is the Solution
Optuno was developed as a solution in light of WordPress’ security deficiencies, and that remains true to this day.
Our CMS code is close-sourced, which means that our in-house developers are the only people with access to it.
Our team also performs regular tests on our updates before we ever submit them to be used by our customers.
Sorry hackers. Optuno is hack-proof. Just ask our customers.
Of course, we don’t ignore the chances of a possible attack. We anticipate it and we always make the right adjustments to keep our customers safe and secure.
Don’t believe us. Here’s how Optuno can prevent possible attacks from hackers.
- Hosting Security - The firewalls on all of our servers are multi-leveled and perform various user tracking functions on top of standard filtering including integration with ModSecurity (mitigates XSS, SQL injection attacks, brute force, etc), SPI (stateful packet inspection), service monitoring (access by FTP, port scans, multiple invalid password attempts) among other various supporting functions. Should anything trigger one of these functions, a block is made automatically.
- Multiple Safeguards - All Optuno accounts include 2x daily backups of our customer's data and are hosted and protected by our sister company EndLayer, LLC in our 71,000 square feet data center. The data center is built to the highest standards – with N+1 power and cooling redundancy, anti-static flooring, wet and pre-action fire protection and advanced proximity and biometric security controls.
And that’s not all!
Here are some more ways we’ve made FICMS® armed to the teeth against hackers.
- Access Restriction Module - With this security module enabled, Optuno customers can Whitelist and/or Blacklist IP addresses from being able to access: a) the website; both front-end and admin users, b) the admin console, and c) includes the ability to make the entire website or various pages or sections completely user/pass protected.
- Brute Force Protection - This security module allows Optuno customers to receive a notification when someone tries to hack into your site by guessing your username or password. The Brute Force Protection module lets you define rules that prevent those attempts. You can also easily create and define your own rules, with varying attempt numbers, ban intervals, etc. Just click “Add New Protection Rule” and specify the parameters: login attempts, captcha display, notification, disable logins, redirect, or ban IP. In addition, you can open the “Brute Force Log” to see a full history of your system’s attempts, catches and bans.
- Login Trade Protection - This security module catches compromised accounts before you lose vital information. Optuno's Login Trade Protection module helps protect your site from leaked usernames and passwords, by detecting when multiple IP addresses are attempting to log in with the same information. Our Login Trade Protection module will then block those addresses and notify you immediately.
- Two Factor Authentication - This security module lets you add an extra layer of security to your site. Two-Factor Authentication (2FA) gives your login system an additional safeguard, requiring a second protection rule before users can log in with a known username or password. When you've enabled two-factor authentication, any user who enters the correct username and password will receive a random 6-character verification code via email or SMS. The user will then have to copy and paste this verification code into the login form before being allowed to enter the site. The user will only be permitted access if the code matches. Get the point?
We’ve gone all out to ensure that our hosting and content management system is impenetrable to hackers.
In fact, Optuno’s proprietary content management system FICMS® has only been around for five years, and it’s designed with state-of-the-art technology that has been used by small businesses, multinational firms, private and publicly traded companies, and even state and local governments.
They all trust Optuno. Why shouldn't you?
The facts above prove that your website isn’t secure with WordPress.
Why don’t you take a proactive approach to improve your web security today by purchasing one of our premium website packages?
Your security and your customers’ security surely depends on it.



 View Printer Friendly Version
View Printer Friendly Version





